DocsAmbassador Cloud
Saved Telepresence intercepts
Saved Telepresence intercepts
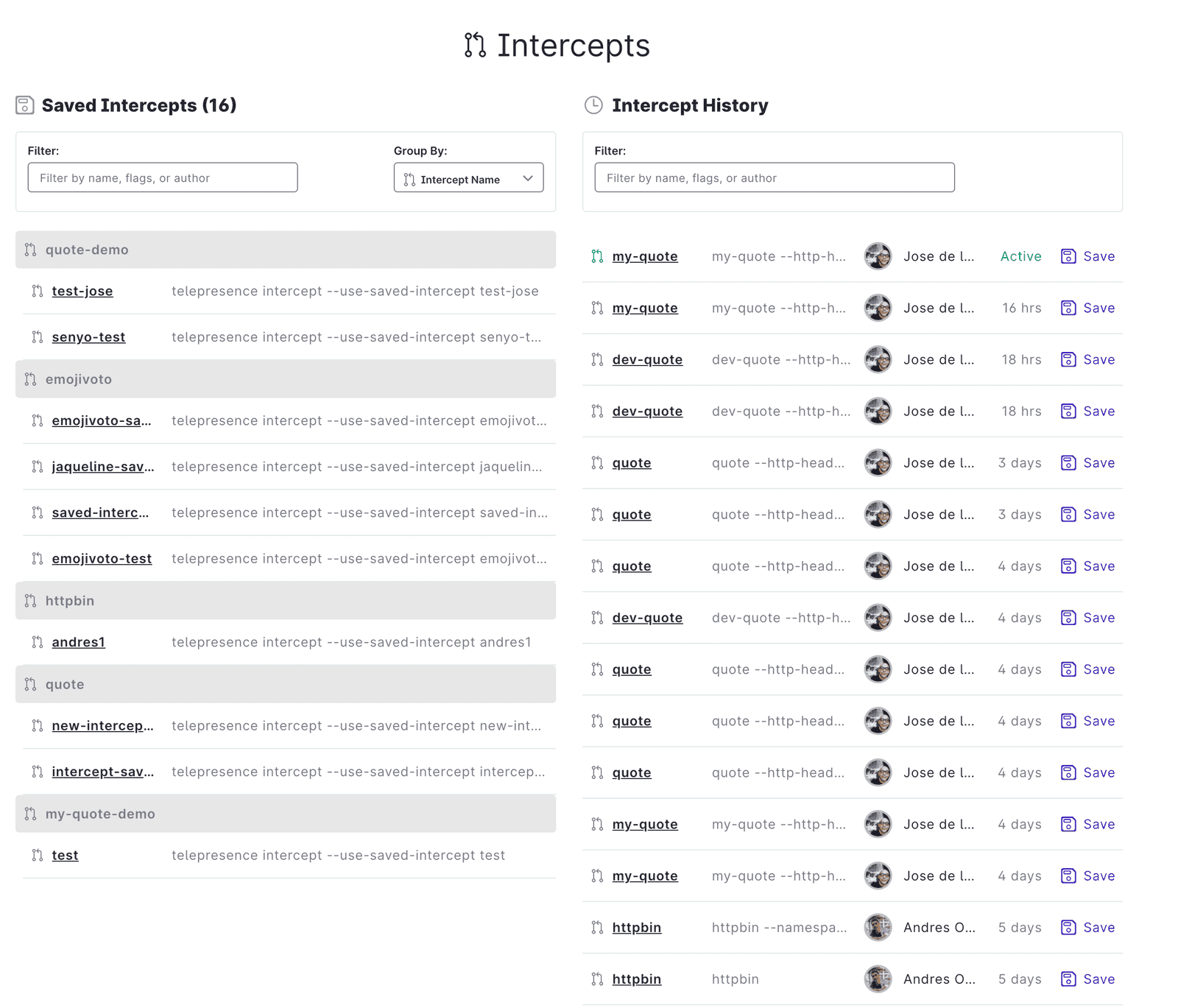
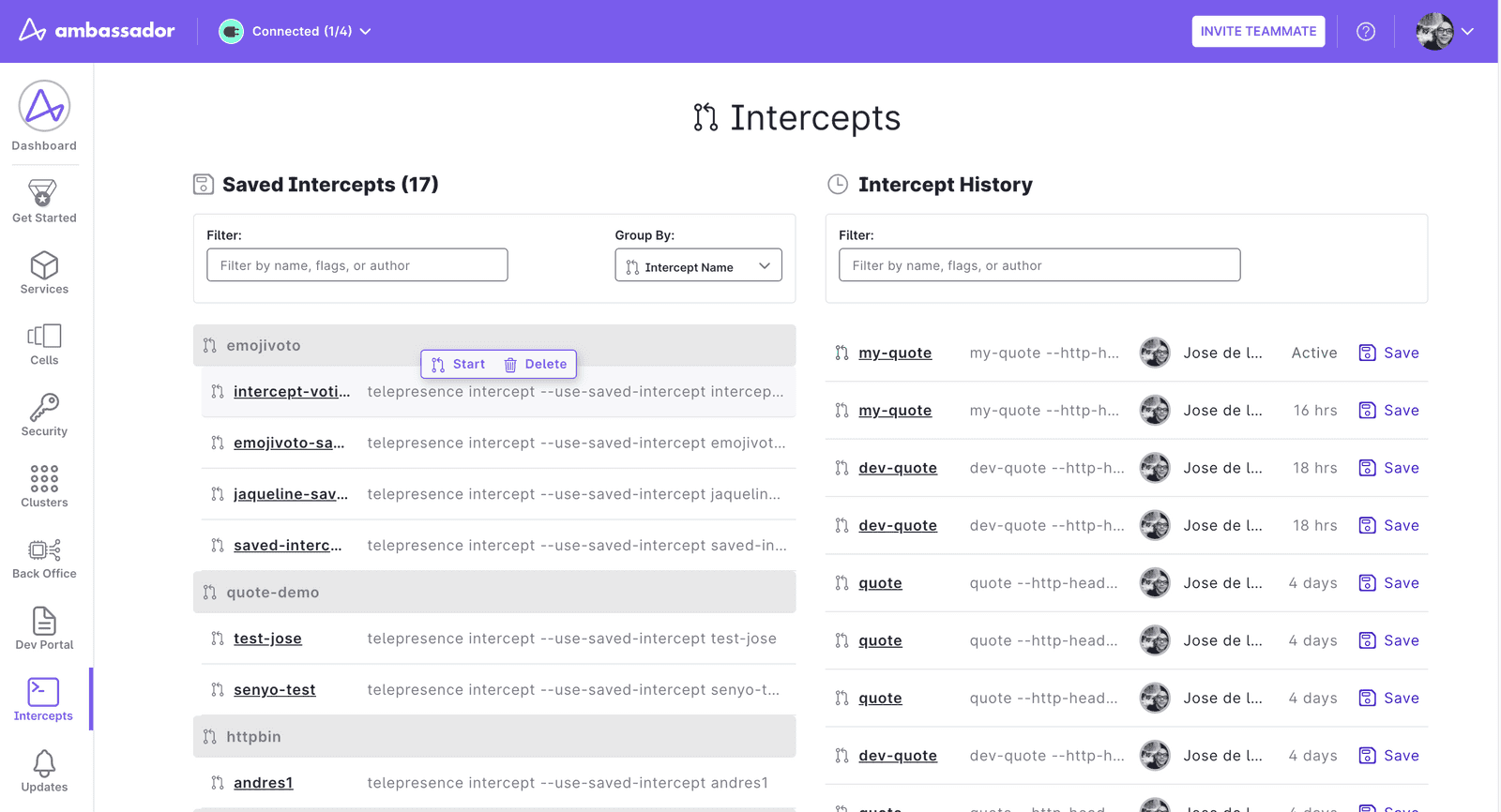
The Ambassador Cloud Intercepts page gives you access to your intercept history and allows save previous intercept configurations. Saved intercepts can be shared with other team members to streamline your development cycle and collaborate more easily.
Prerequisites
To use the saved intercepts feature, you need:
- A local installation. of Telepresence version 2.7.0 or later.
- An Ambassador Cloud account.
- Access to a Kubernetes cluster.
Telepresence releases prior to version 2.7.0 don’t support the saved intercepts feature. If you are using an older version of Telepresence, visit the upgrade page to learn how to update to the current version.
Creating and saving intercepts
Intercept configurations are automatically saved in the Intercept History tab on the Intercepts page. To save an intercept and share it with team members, follow the steps below.
- Run
telepresence loginto authenticate yourself in Ambassador Cloud. - Run
telepresence connectto connect Telepresence. - Intercept traffic to a service running in your Kubernetes cluster by creating an intercept. For example:Each time you create an intercept like this, it is logged in Ambassador Cloud's Intercept History.
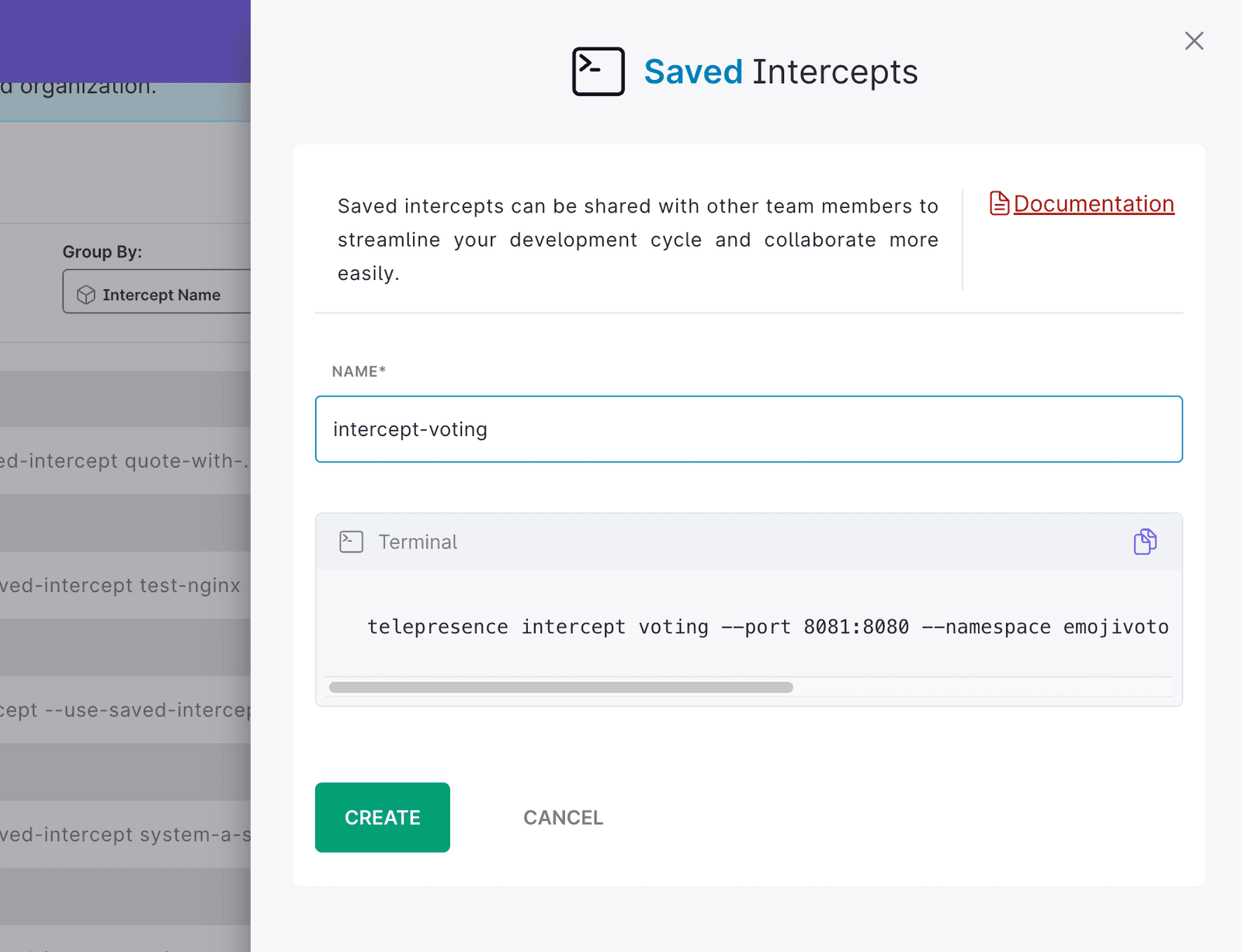
- Go to the Ambassador Cloud Intercept page, in the right side you will see a list called
Intercept Historynow click on the intercept you just created. Enter a name for the intercept and click Create. - The incercept is now available in the Intercepts page in the left side of the page, you will see a list called
Saved Intercepts.
Using saved intercepts
Once an intercept has been saved, you can reuse it and share it with team members. You can also create more intercepts with the same set of arguments as in the original saved intercepts by with the following command:
This command fetches the intercpet configuration of the saved intercept and uses it to run a new intercept. This way, you don't need to remember all the arguments required to intercept a service in a particular cluster. sence CLI version v2.7.0 or later.
Managing Saved Intercepts
In the Telepresence Saved Intercepts page on Ambassador Cloud, you can see the list of saved intercepts created by any Ambassador team member. For each of these intercepts, you can:
- inspect its author, creation date and flags.
- delete the saved intercept.
- see the command as it would be entered in the CLI.